We have designed and developed a triple-layer cybersecurity solution to help protect our clients’ data and devices from viruses, malware, ransomware, malicious attacks, and data loss for the 99% of times.
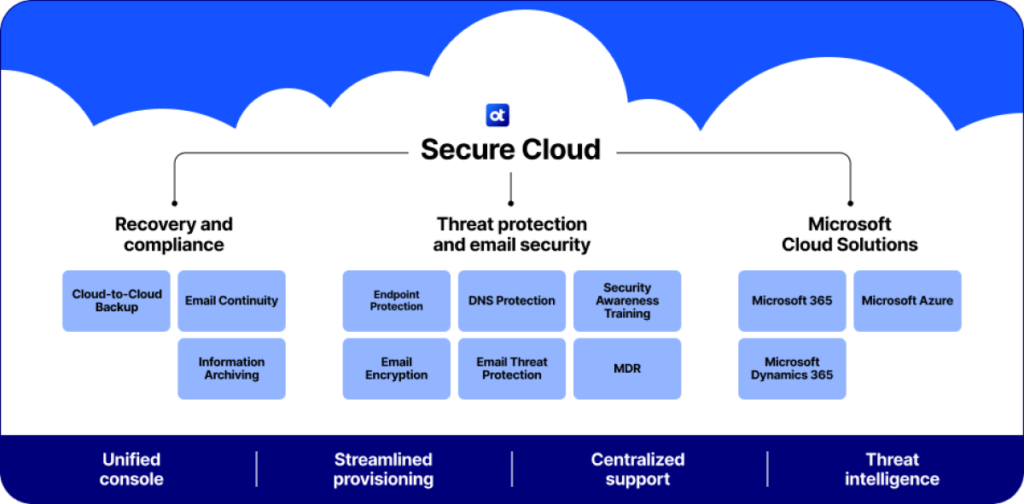
Our solution starts with Endpoint Protection that helps safeguard email accounts with encryption against phishing, malicious codes, and redirecting links. Secure browsing with pre-checked URL reputation reporting.
DNS protection that helps block access to a majority of known high-risk websites as well as the ability to monitor and block inadvertent access to redirected websites from email links. Security monitoring and reporting is enabled and handled on a 24x7x365 basis with a team in The USA.


We also bring you simulated phishing attacks and online short video based self-paced cybersecurity training to educate and empower you against all the threats of the internet security in the real world.
Our Cybersecurity’s innovative new threat detection approach combines AI (Artificial Intelligence) with machine learning models that automatically and continuously learn with rapid deployment—allowing new threat detection models to be in place within hours to protect from new and evolving threats.

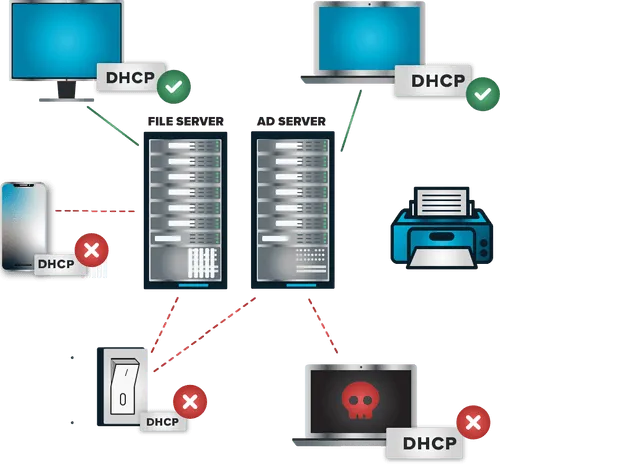
Our next phase brings a Zero Trust cybersecurity platform that protects devices from any unauthorized software installations, even surpassing generic drive encryption. Get ironclad Zero Trust cybersecurity with granular control over every app, script, and process in your environment. Welcome to a world with fewer alerts, less blind spots, and a new level of control — all backed by unmatched 24/7 support.
Network Control is a firewall for endpoints and servers that can be managed centrally. It provides complete control over network traffic, which helps to protect your devices. Custom-built policies are used to grant access to the network based on IP address, specific keywords, agent authentication, or dynamic ACLs. This network access security tool allows granular control over access to the network.
The Network access control solution helps protect business assets whether employees are in the office or remote. It provides a direct connection between the client and server, as opposed to a VPN that goes through a central point.
AllowListing, RingFencing, & Network Control are a few other important features that help identify and allow safe and secure application to be installed on network devices after they have been tested in a safe, secure, and isolated environment on our network just prior to installing them on yours.

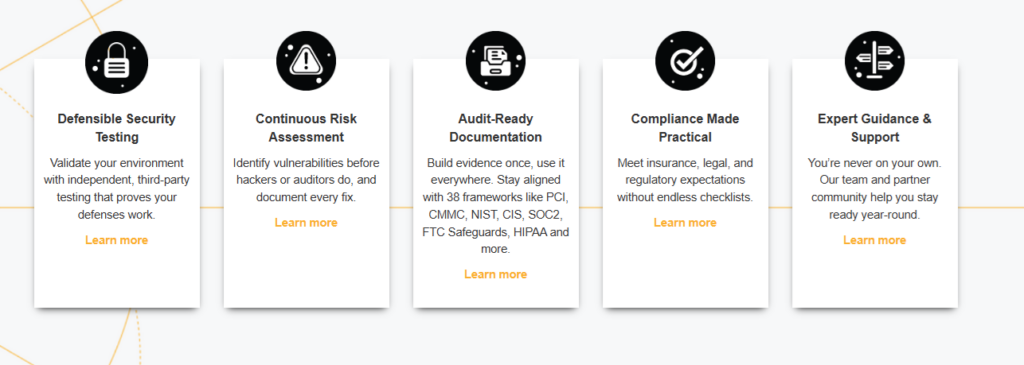
Lastly, we implement a CLE (Cyber Liability Essentials) and CW (Cyber Watch) system that produces regular penetration testing to expose vulnerabilities in the entire network with the industry leading recommendations to apply the appropriate measures to tighten up the security defenses.
The key components to this phase are: Independent third-party validation, Audit-ready documentation, Clear, actionable reporting, Expert guidance, and Defensibility that lasts.
Creating an IRP (Incident Response Plan) to put in place for that just-in-case of the 1% of situations will activate a set of SOPs (Standard Operating protocols) to counter the incidents to remediation and recovery and further protection. All these steps will work toward creating and providing proof of compliance for those clients who are required to show a variety of levels of industry required compliance. We protect our clients so that they can protect their clients.
Contact us for a FREE quote to Secure your network infrastructure.

